There’s always a lot of confusion on exactly how to use CCMSETUP and the various switches and properties for it even though it’s fully.The first thing to note about CCMSETUP is that it is used for all client agent installation activity (except client agent installation from WSUS). Yes, even client push uses CCMSETUP.
Basically, client push simply delivers CCMSETUP to target systems and starts it. What that ultimately means is that no matter how you install the client, it’s always the same process so there is no technical difference between any of the methods (except using WSUS as mentioned).Next, it’s important to note that CCMSETUP is simply a bootstrapper that in turn initiates a handful of other things including the following (this isn’t an exhaustive list, just the main relevant points for this discussion):. Copies itself to C:Windowsccmsetup, installs itself as a service, starts that service, and then immediately exits. Why would it do this?
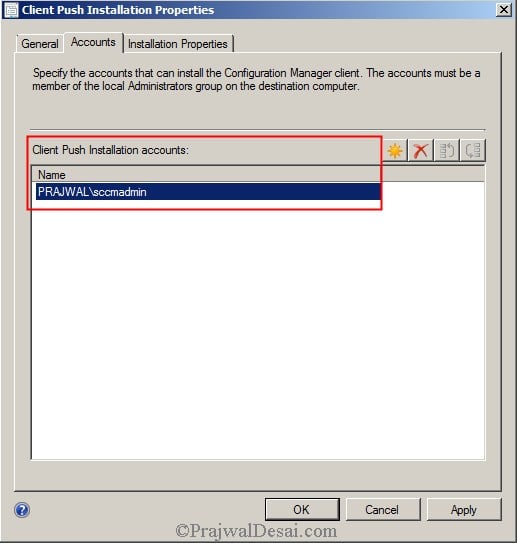
Sccm Client Push Installation Properties
Reboot resilience. Thus, if the system reboots for whatever reason without CCMSETUP actually finishing the entire installation process, it will restart after the reboot automatically. The main ramification to keep in mind here is that that service runs as the local System account.
That means that if CCMSETUP needs access to anything else on the network, it will use the AD computer account of the system. If the system is not a member of a domain, it has no AD computer account to use (obviously) and thus won’t be able to authenticate as anything other than anonymous. Downloads prerequisites – like.Net Framework 4.0 client profile and Silverlight — and other files needed to install the client – like client.msi — and installs prerequisites not already installed on the system.Where does it download these from? By default (in 2012), CCMSETUP locates an MP using normal MP location rules (AD, DNS, WINS) and then asks the MP for the closest DP. Then, using BITS, it downloads the files using BITS from the DP returned by the MP which follows normal content location rules which are purely based on boundaries within content distribution boundary groups.
If for whatever reason, no valid DPs exist or are available for the target system based upon the boundaries, the files will be downloaded from the MP itself. Note that this BITS download will work fine for anonymous clients – like those in a workgroup or untrusted domain and does not require any special permissions or access. Finally, it installs the client agent from the locally downloaded files by initiating the install using client.msi.That brings us to /mp and SMSMP. Both are valid on the CCMSETUP command-line, but both are completely different in multiple ways. /mp“Options” like /mp that are prefixed with a forward-slash are parameters for CCMSETUP itself.
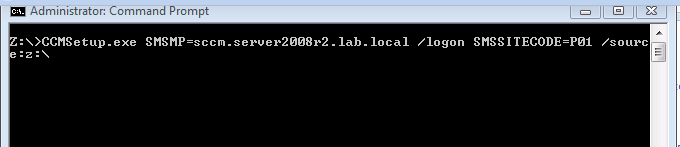
Thus, they control or affect the behavior of CCMSETUP and not the client agent. So, even though /mp contains the letters ‘m’ and ‘p’, this does not in any way mean that it sets the MP for the client agent.
Ccmsetup Command Switches
What /mp actually does is instruct CCMSETUP which MP to use to query for a DP (as mentioned above) thus bypassing the normal MP lookup.Multiple MPs can be specified using /mp by separating them with a semi-colon (this enables the lookup to try each MP in order if the availability of the MPs is a concern): ccmsetup.exe SMSMP=if an MP requires HTTPS communication, you should specify the prefix in URL format including the protocol: ccmsetup.exe SMSMP=is always a good practice to use the full FQDN and ensure that name resolution is working for this name on the target clients. If name resolution is not working, you’ve got bigger problems that CCMSETUP cannot magically solve. Note also that CCMSETUP setup parameters require a colon between the option name and the value specified for that option. SMSMP“Options” like SMSMP that are in all capital letters are public properties that are not processed or used in any way by CCMSETUP but are instead passed directly to client.msi when CCMSETUP executes it. Thus, these properties do directly affect the client agent and its configuration. Note that you don’t actually have to specify the properties in all capital letters on the command-line, but it is best to do this so that they clearly stand-out.SMSMP specifies the initial MP that the client agent uses (“initial” because with 2012, we can have multiple MPs within a single primary site and this will rotate periodically on clients). Without SMSMP, the client agent relies on normal MP location processes (AD, DNS, WINS) just like CCMSETUP does to initially set the MP that the client agent will use.As with /mp, you should use the full FQDN of the MP and if an MP uses HTTPS, you should also specify the name of the MP in URL format including the prefixed protocol: ccmsetup.exe SMSMP=ccmsetup.exe SMSMP=/mp, you can only specify a single MP with SMSMP.
Also, public properties are not prefixed with a forward-slash and use an equals sign to set the value of the property.One thing to make sure of is that you specify all CCMSETUP parameters on the command-line before you specify any public properties. This simply has to do with how CCMSETUP parses the command-line: it assumes that all parameters come first so as soon as it encounters a property, it stops looking for any more parameters.You can, of course, use both of these options together which is common because the reason for using them is the same: you don’t want to (or can’t) rely on normal MP lookup. If MP lookup is working, then there’s no reason to use either. The only time to really expect any issues with MP lookup is when the target client is untrusted like when it’s in a workgroup. Hi Jason, I hope you are still checking this post (it’s been already a year since your last reply.I would need your help to clarify for me what should I do nowadays, running SCCM 1610 with full HTTPS and running Windows 10 Baremetal using PXE.I’ve got the Workstation Certs exported with Private Keys.Problem:Scenarios:“Baremetalling” a current workstations which AD object and SCCM device object are present: ConfigMgr Client Certificate was already in place before Baremetal.I am able to finish a baremetal, however the PC, however. Even though the certificate is still in Certificate store (MMC), the SCCM client shows PKI: none.Solution: Simply delete the current COnfigMgr Client Certificate and request it back from AD.
Restart SMSAgent Host, and finally SCCM client is back to PKI.For some reason, I believe that During baremetal, the certificate doesnt get upgrade or overwritten by the OSD process (I can confirm that because when I first log in to the PC and I open MMC, the expiration date is wrong, it is old related to the first installation day of the PC. I expected the new certificate to be installed.With refresh scenario where PCs in both AD and SCCM are active, I also have the same issue. OSD finishes 100%, however SCCM local client shows PKI=none.Only a reboot doesnt fix the issue, I have to delete the old ConfigMgr Client certificate in order for the SCCM client to show PKI.I might have missing something.I believe I have to add the current Client workstation certificate to my boot image, which I havent done because I couldnt find how, instead I have created a new unattend.xml file from the 1607 Windows 10 image I am deploying which i am running certutil to install the certificate and using the private key and passwd. I have added that custom unattended.xml file to my “Apply operating system image” Step on my TS. (Is that right?)I believe once I have done the unattended.xml file installing the PFX, I dont need to inject the PFX to my boot, right?Now last question is regarding the ConfigMgr properties.I have added this to my Set up Windows and ConfigMgr/UsePKICert /NoCRLCheck /MP: DNSSUFFIX=mgcorp.co CCMHTTPSSTATE=31I havent changed my SCCM client package, it is still using default properties (Should I also change there or Task Sequence properties will take precedence?Thank you in advance if you ever see this post.
SCCM Firewall ports and network ports must be defined if you want manage clients across multiple networks. Configuration Manager to properly manage clients if some ports are not been defined and opened to allow for traffic to flow properly. Typical symptoms of failed network connectivity can be clients stuck with old configuration manager client, trouble to patch and deploy software. Here is a copy of my cheat-sheet that I use (or send to the network technicians) to make sure all required traffic is let through.